What Happened
A Bitcoin holder reportedly recovered an old wallet worth around $400K after being locked out for 11 years, and Claude was the key helper. The viral framing is “AI brute-forced 3.5 trillion passwords,” but the more accurate version is less cinematic and more useful: Claude helped orchestrate a constrained recovery process from partial clues, old files, and remembered password patterns.
That distinction matters. This was not Claude magically breaking Bitcoin encryption. It was workflow intelligence applied to a hard search problem where the user had fragments of truth: possible password structure, old wallet artifacts, and historical context about how they created credentials years earlier.
In other words, AI did what good operators do at scale: organize uncertainty, generate hypothesis sets, prioritize attempts, and keep iteration disciplined over a very large search space.
What Claude Actually Did (and Didn’t Do)
The story gets misunderstood when people collapse everything into “AI hacked a wallet.” That’s not what happened. If reports are accurate, Claude helped with structured candidate generation and recovery strategy, not cryptographic breakthrough.
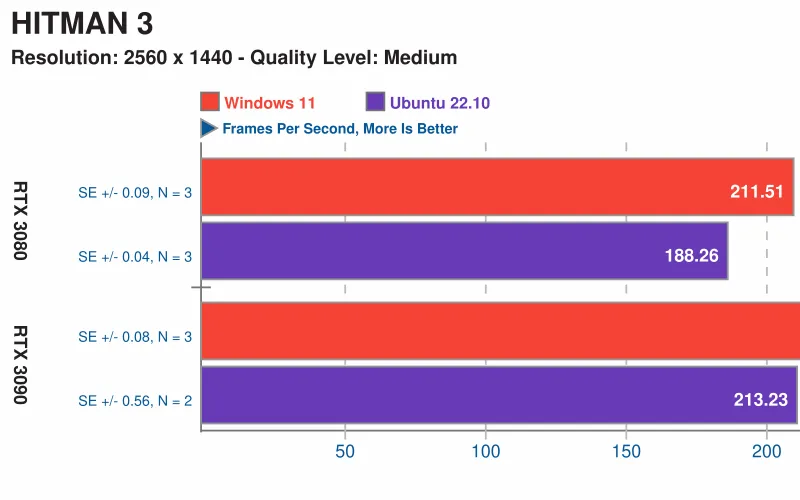
Think of it as intelligent brute-force orchestration, not brute-force invention. Raw brute force without constraints is usually useless because the search space explodes. What made this viable was constraint-solving: using memory fragments, language patterns, old naming habits, likely substitutions, date anchors, and file history to reduce dead-end attempts.
Claude likely added value in three places: generating better candidate trees than a human would manually maintain, sequencing attempts to maximize early hit probability, and continuously refining strategy based on failure feedback. Humans are good at intuition. Models are good at systematic expansion without fatigue. Combined, that can unlock problems that sit unsolved for a decade.
Why This Matters Beyond Crypto
This is not fundamentally a Bitcoin story. It is an operations story about AI as a coordinator for computationally expensive, constraint-heavy tasks.
Credential recovery, legacy archive access, encrypted backup restoration, key material triage, forensic reconstruction, and historical data migration all share the same shape: huge possibility spaces, partial evidence, and high value per successful recovery. That is exactly where modern models can create outsized ROI.
People still treat AI as a chat interface for writing text. Stories like this show the better framing: AI as a planning and orchestration layer over tooling. The model doesn’t need to “be the tool.” It needs to route steps, manage hypotheses, and keep the process coherent while external systems do the heavy compute.
That is the real capability signal here: not “AI cracked encryption,” but “AI handled long-horizon, high-complexity workflow management under real constraints.”
The Business Angle Is Bigger Than It Looks
There is a serious B2B opportunity in AI-assisted recovery services. Most companies have expensive “digital dead zones”: old encrypted archives, inaccessible credential vaults, abandoned infrastructure accounts, corrupted backups, and undocumented key rotation history.
Today, those incidents are handled by expensive specialists with inconsistent process quality. An AI-assisted recovery pipeline can standardize candidate generation, evidence tracking, attempt ordering, and audit logs. That makes outcomes more repeatable and often faster.
The margin profile can be excellent because the customer value is tied to asset recovery, downtime reduction, and risk mitigation. If you can recover a seven-figure archive or restore access to a business-critical system, pricing is value-based, not hourly commodity consulting.
This also creates recurring revenue possibilities: ongoing credential resilience audits, recovery-readiness testing, key hygiene monitoring, and disaster recovery simulation. Recovery doesn’t have to be a one-time emergency business. It can become a continuous assurance product.
What Founders and Security Teams Should Do Next
First, stop thinking in terms of “can AI crack things?” and start thinking in terms of “can AI shrink search spaces safely?” That mindset shift immediately opens practical use cases without crossing legal or ethical boundaries.
Second, build a constrained recovery framework instead of ad hoc scripts. The core stack is straightforward: evidence ingestion, pattern extraction, candidate generation, prioritization engine, execution harness, and strict logging. The AI sits in orchestration and hypothesis refinement, while deterministic tooling handles cryptographic checks and verification.
Third, treat governance as a product feature, not paperwork. Recovery workflows touch sensitive assets, so you need authorization controls, chain-of-custody records, rate limits, and clear user consent boundaries. The commercial winners here will be the teams that combine high recovery success with enterprise-grade compliance posture.
Fourth, invest in “memory artifact mining.” In many recovery cases, success comes from forgotten context: old notebooks, naming conventions, legacy file trees, prior password schemas, or historical account metadata. AI is excellent at extracting pattern signals from messy personal or organizational history.
What Not to Do
Do not market this as encryption breaking. It is inaccurate and invites legal and reputational problems. Position it correctly as authorized recovery with known ownership and partial evidence.
Do not run unrestricted brute-force loops without clear legal boundaries. Jurisdiction, ownership proof, and explicit client authorization are non-negotiable in this category.
Do not assume model intelligence replaces domain tooling. AI can improve strategy, but cryptographic validation, filesystem forensics, and operational security still require specialized infrastructure.
And do not skip post-recovery hardening. Once access is restored, rotate credentials, re-encrypt backups, document recovery paths, and remove single points of failure. Recovery is a chance to eliminate the conditions that caused lockout in the first place.
What This Says About Claude Specifically
The strongest signal is not raw “IQ.” It is stamina plus structure. Claude appears useful when tasks require long iterative loops, careful bookkeeping, and strategy adjustment over many failed attempts. That is exactly the profile of many enterprise workflows that humans find tedious and error-prone.
If this pattern keeps showing up, Claude’s competitive edge in business contexts may be less about one-shot brilliance and more about reliable orchestration in multi-step operations. That’s where organizations actually spend money.
Bottom Line
The $400K wallet recovery story is important because it demonstrates a practical AI pattern: smart constraint-solving can turn impossible-seeming brute-force problems into solvable workflows when ownership and partial context exist.
The takeaway for builders is clear. Don’t chase “AI hacks encryption” fantasies. Build authorized, auditable, constraint-driven recovery systems where AI handles planning and iteration, and deterministic tools handle verification.
That is the real opportunity: high-trust, high-margin AI recovery infrastructure for credentials, wallets, archives, and enterprise access failures. The crypto headline is just the loudest example of a much larger market opening.
Now you know more than 99% of people. — Sara Plaintext