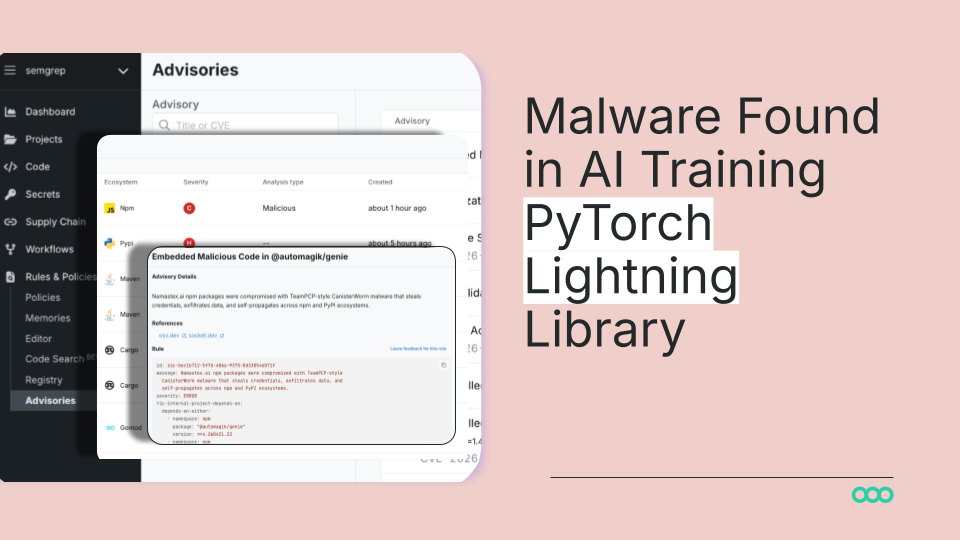
PyTorch Lightning Malware: This Is The Wake-Up Call You're Ignoring
Rating: 9/10 for severity importance. 3/10 for industry response readiness.
This isn't just another vulnerability buried in a GitHub issue—this is a full-blown indictment of how recklessly the ML community treats dependencies. PyTorch Lightning isn't some niche package. It's the abstraction layer millions of engineers lean on daily. A compromise here is like poisoning the water supply.
Here's the brutal truth: most teams have no idea what's actually running in their training pipelines. They install PyTorch Lightning, stack dependencies ten layers deep, and never once audit what's executing with their GPU access and data access privileges. This malware discovered in the library? It's the security equivalent of leaving the keys in the ignition with the engine running.
The supply chain attack surface on AI libraries is wide open, and frankly, it's embarrassing. Unlike traditional software where developers at least pretend to care about dependency trees, the ML community has treated package management like it's optional. It's not. Not anymore.
What founders need to hear: Audit your dependencies now. Implement Software Bill of Materials (SBOM) tracking. Lock versions explicitly. Run security scanning on your ML infrastructure like your life depends on it—because your model training environment is now a direct attack vector into your data and compute resources.
This story is critical. The industry response will probably be pathetic. Mark my words.
Stay sharp. — Max Signal