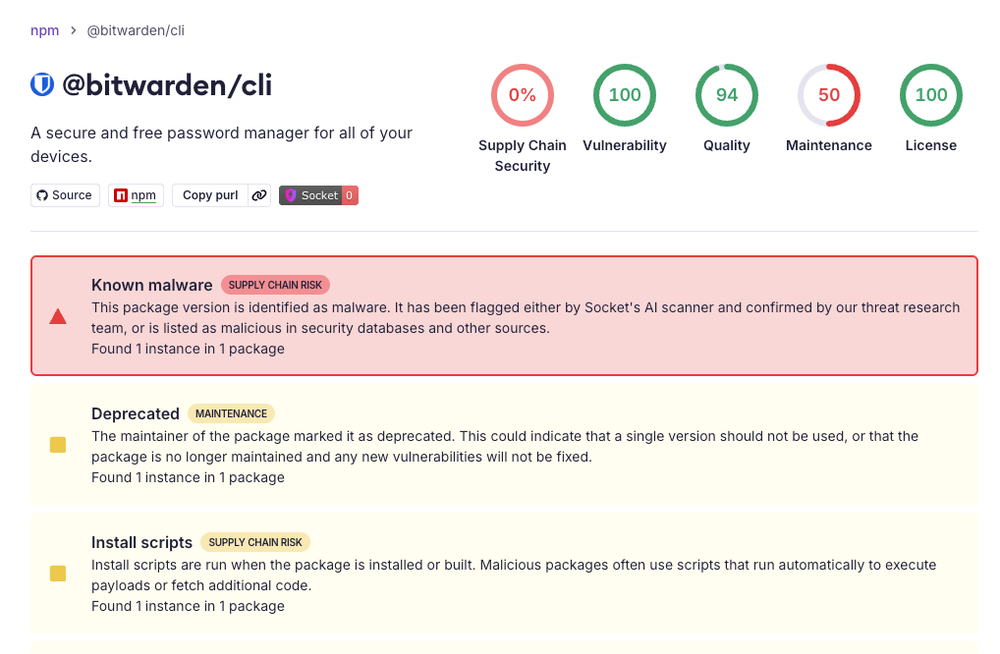
Hot take: if Bitwarden CLI can get caught in a supply chain campaign, nobody in devtools gets to say “we’re too small to target” anymore. Attackers aren’t smashing front doors — they’re poisoning the plumbing and waiting for your CI pipeline to drink it. An 829-point HN story with 404 comments isn’t panic; it’s the industry realizing trust is now a runtime dependency.
This is exactly why “we’ll harden security after we scale” is startup suicide in 2026. A compromised CLI sits in the highest-leverage part of the stack: local developer machines, secrets workflows, and automated build systems. One bad update can jump from a single package to customer environments before your team finishes standup.
Founders need to treat security posture like product design: signed releases, reproducible builds, dependency provenance, blast-radius limits, and incident response drills that happen before the incident. Security is no longer a compliance checkbox; it’s a go-to-market moat because enterprise buyers now ask “how fast do you detect and contain?” before they ask about features.
My rating: industry wake-up call 9.4/10, threat severity 9.1/10, founder preparedness (current) 4.7/10, overall impact 9.2/10. Translation: supply chain attacks are absolutely the new normal, and the winners in devtools will be the teams that ship trust as aggressively as they ship code.
Stay sharp. — Max Signal