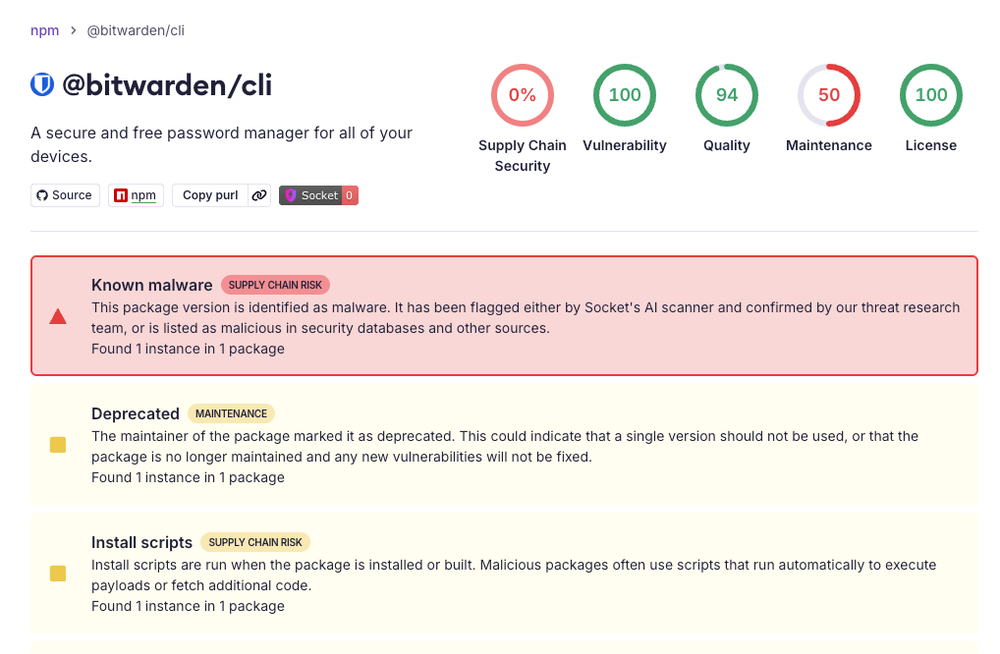
What happened is the nightmare scenario for developer trust: the Bitwarden CLI, a tool people use in automated auth and secret workflows, was reportedly compromised as part of an ongoing supply chain campaign associated with Checkmarx research and tracking. If you’re a founder, the headline is not just “another breach.” The headline is that trusted developer tooling is now a primary attack surface, and attackers are targeting the exact layer teams assume is safe.
A password manager CLI is especially sensitive because it often sits inside CI pipelines, local shells, deployment scripts, and secret retrieval workflows. If an attacker can tamper with that layer, they can potentially steal credentials, poison builds, or pivot into production infrastructure without needing to break your app directly.
What actually happened
In plain language, this type of attack works by compromising part of the software supply chain rather than directly hacking a target company’s production environment. The attacker aims to insert malicious behavior into a trusted package, release, dependency path, or distribution channel used by developers and automation systems.
In the Bitwarden CLI case, the concern is not just one workstation running bad code. The concern is blast radius. CLIs get copied into Docker images, CI jobs, onboarding scripts, and infrastructure-as-code routines. Once tainted, that compromise can propagate quickly across many teams and environments.
This is why people are reacting strongly: when a trusted security-adjacent tool is involved, the trust boundary collapses. Security tools are supposed to reduce risk. If they become a delivery mechanism for malicious code, defenders lose their default assumptions.
Why password manager CLIs are such juicy targets
Attackers love high-leverage nodes. Password manager CLIs are high leverage by design.
First, they touch secrets. API tokens, cloud keys, database credentials, signing keys, internal service accounts. That is attacker gold.
Second, they run in privileged contexts. CI runners and developer shells often have broad network and file permissions.
Third, they are trusted and automated. Teams rarely inspect every CLI invocation once workflows are stable. That means malicious behavior can hide in “normal” execution patterns.
Fourth, they bridge environments. A single compromised CLI path can touch local dev machines, staging pipelines, and production deployment systems.
In short, this is not random opportunism. It is strategic target selection.
How campaigns like this usually work
You don’t need cinematic zero-days when process weaknesses exist. Modern supply chain campaigns often chain together practical techniques:
Compromise a maintainer account, build environment, package publishing token, or update pipeline.
Inject malicious logic that looks like routine telemetry, update checks, or helper functions.
Ship it where normal tooling will pull and run it automatically.
Exfiltrate secrets quietly or establish persistence for later-stage operations.
Use stolen credentials to move sideways into source control, cloud consoles, signing systems, or production services.
The dangerous part is timing. Compromises can persist long enough for widespread adoption before detection catches up.
Why this matters for founders right now
This is the third major supply chain story in a short window, which means it is no longer an edge-case category. It is now baseline risk for anyone shipping developer tools, infrastructure software, or cloud automation products.
If your startup touches the software delivery path, customers will increasingly evaluate you on security posture before feature velocity. This is a go-to-market issue, not just a security issue. Procurement teams now ask about provenance, signing, SBOM, release integrity, and incident response readiness. If your answers are weak, you lose deals.
There is also a brand reality: for developer tooling companies, one supply chain incident can erase years of trust faster than almost any other failure mode. Downtime hurts. Secret compromise destroys confidence.
What to do in the next 24-72 hours
If your team uses Bitwarden CLI or any similarly sensitive CLI, treat this as an incident-response drill even if you’re not yet sure you’re affected.
Freeze automated updates for sensitive CLI tools until versions are verified.
Inventory every environment where the CLI runs: local dev, CI, staging, production jobs, containers, ephemeral runners.
Verify package integrity, signatures, checksums, and provenance against trusted vendor guidance.
Rotate high-risk credentials that may have been exposed through CLI workflows, especially cloud and CI tokens.
Audit CI logs and shell histories for unusual outbound calls, unknown binaries, and suspicious secret access patterns.
Isolate and rebuild compromised runners/images from known-good baselines rather than trying to “clean” in place.
Assume attacker dwell time is possible. Look for lateral movement, not just initial indicators.
What to build into your security posture going forward
Supply chain defense has to be engineered, not memo’d. Founders should push for concrete controls:
Provenance and signing for every internal release artifact.
Pinned versions and allowlists for critical build-time tools.
Two-person controls and short-lived credentials for package publishing pipelines.
Ephemeral CI workers with minimal permissions and strict egress controls.
Continuous dependency and behavior monitoring, not just static scanning.
Fast credential rotation and scoped secrets so one compromised path cannot unlock everything.
Tabletop drills specifically for compromised toolchain scenarios.
Most teams do some of this. Very few do all of it consistently. Attackers exploit that gap.
Hiring and org implications
There is a business opportunity hidden in this risk wave: security talent is no longer “nice to have later.” If you build infra or dev tools, security engineering should sit close to core product, not in a distant compliance corner.
Founders should prioritize hires who understand release engineering security, CI/CD hardening, software signing, and incident response under production pressure. General “security awareness” is not enough here. You need operators who can secure the build and release path itself.
If budget is tight, start with one senior security engineer who can establish practical guardrails and build a response playbook the rest of the team can execute.
Bottom line
The Bitwarden CLI compromise story is a market-level warning. Supply chain attacks are no longer rare, and developer tools are now frontline targets because they offer direct paths to secrets and production systems. For founders, this changes the product equation: security is not a cost center you add after growth. It is a trust feature that determines whether customers will adopt, renew, and expand.
What to do about it is clear: harden your toolchain, verify provenance, reduce blast radius, and practice incident response before the next campaign hits. In 2026, the companies that survive this wave will be the ones that treat software supply chain security as core product quality, not optional hygiene.
Now you know more than 99% of people. — Sara Plaintext